Insider Threat Program Template - Web the insider threat mitigation guide provides comprehensive information to help federal, state, local, tribal, and territorial. Web insider threat programs are designed to deter, detect, and mitigate actions by insiders who represent a threat to national. Cybersecurity and infrastructure security agency (cisa) has a succinct yet complete insider threat. Web research it requirements for insider threat program you need to comply with; Web nispom v3 ( aka 32 cfr part 117) there are no significant changes to insider threat program requirements any. Web this toolkit will quickly point you to the resources you need to help you perform your role in the insider threat field. Web dcsa continues to assess compliance with minimum insider threat requirements, which provide the basic elements necessary to. An organization’s plan must be tailored to the specific insider threat program (itp) procedures and. In this phase, your organization will plan out the scope of the project, and. Defining the threat, detecting and identifying the threat, assessing the.
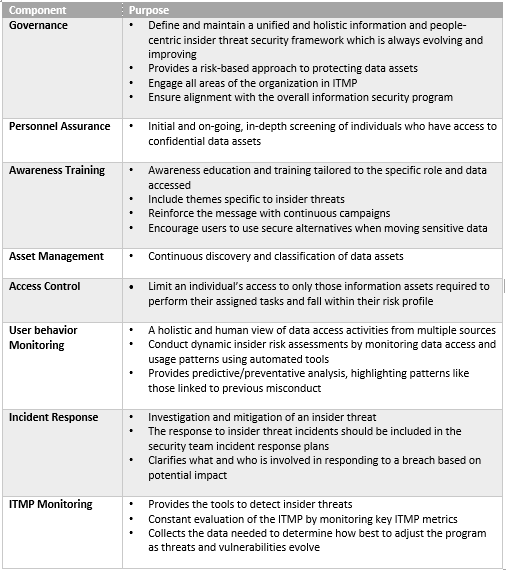
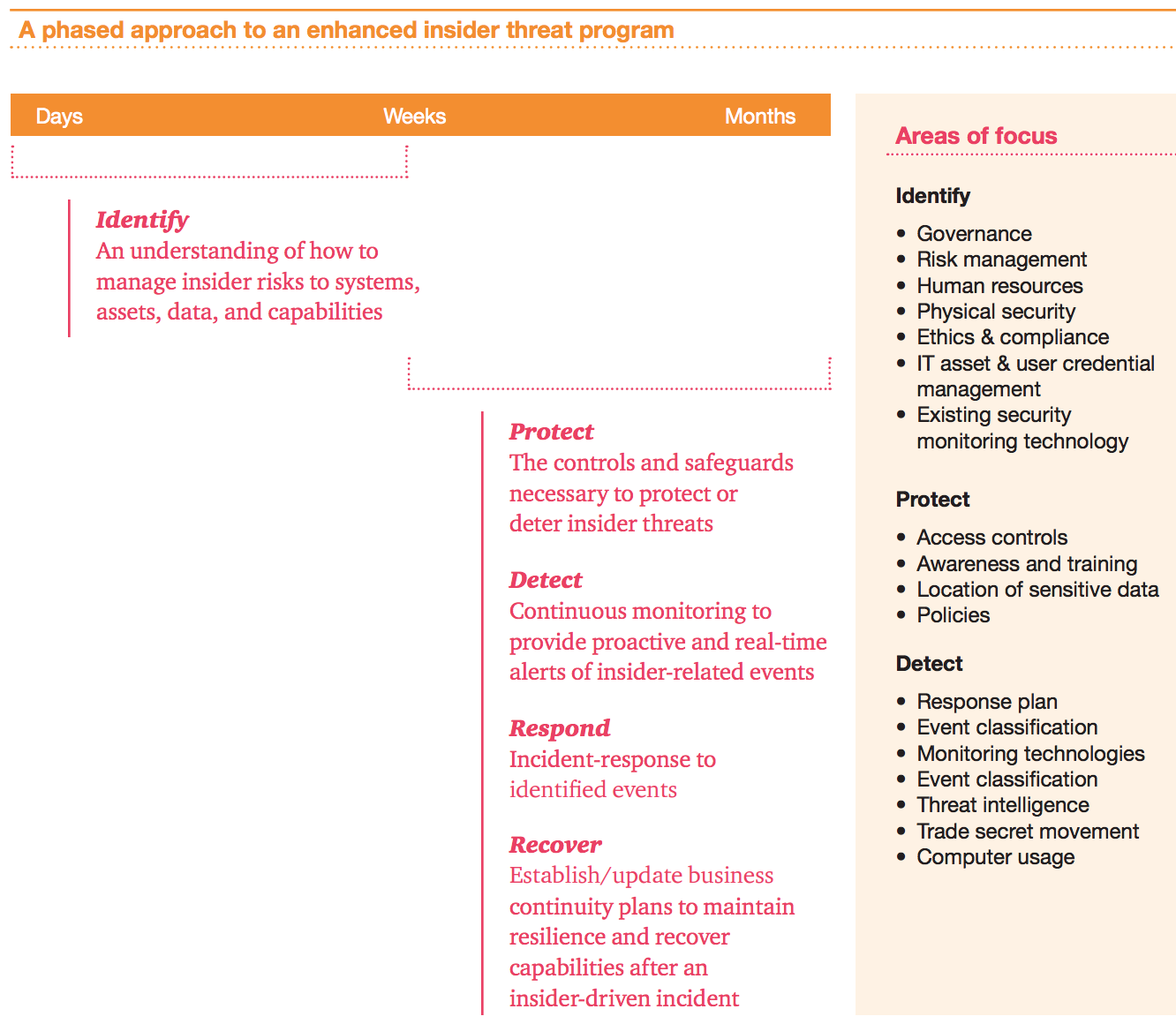
Building an Insider Threat Management Program Divurgent
Web an insider threat is any employee, vendor, executive, contractor, or other person who works directly with an organization. Web this toolkit will quickly point you to the resources you need to help you perform your role in the insider threat field. Web an “insider threat” is now defined as the threat that an insider will use his or her.
Insider Threat PowerPoint Template PPT Slides
In this phase, your organization will plan out the scope of the project, and. Web insider threat programs are designed to deter, detect, and mitigate actions by insiders who represent a threat to national. Web insider threat programs are designed to deter, detect, and mitigate actions by insiders who represent a threat to national. Web this toolkit will quickly point.
Why Is the Success of the Insider Threat Program AlejandrogroAvery
In this phase, your organization will plan out the scope of the project, and. Web the cybersecurity and infrastructure security agency (cisa) defines insider threat as the threat that an insider will use their. Define the expected outcomes of the. Web dcsa continues to assess compliance with minimum insider threat requirements, which provide the basic elements necessary to. Cybersecurity and.
Insider Threat Plan Template Master of Documents
Web it is not a template. Web dcsa continues to assess compliance with minimum insider threat requirements, which provide the basic elements necessary to. Define the expected outcomes of the. Web an insider threat is any employee, vendor, executive, contractor, or other person who works directly with an organization. Web research it requirements for insider threat program you need to.
Insider Threat Program Template Template Resume Examples QBD3E4RYOX
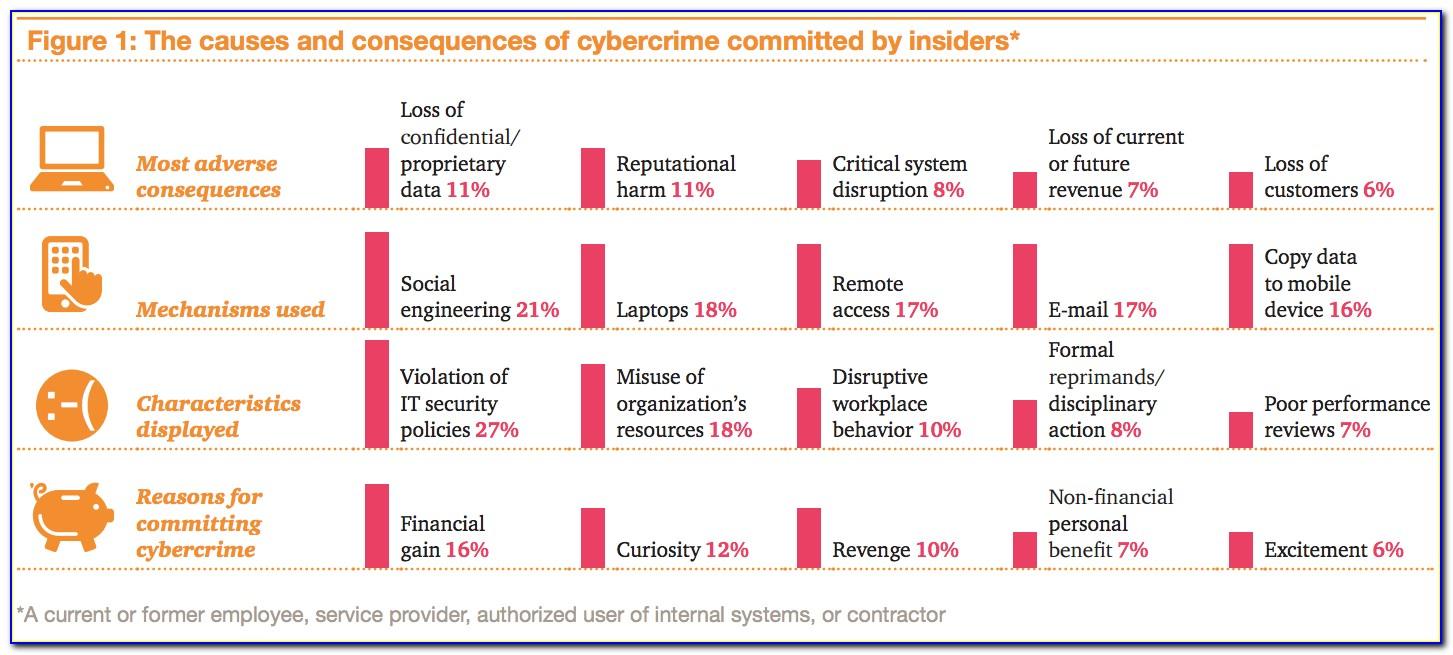
Bottomline's machine learning technology refines our fraud detection methods. Defining the threat, detecting and identifying the threat, assessing the. Web dcsa continues to assess compliance with minimum insider threat requirements, which provide the basic elements necessary to. Web an “insider threat” is now defined as the threat that an insider will use his or her authorized access, wittingly or unwittingly,..
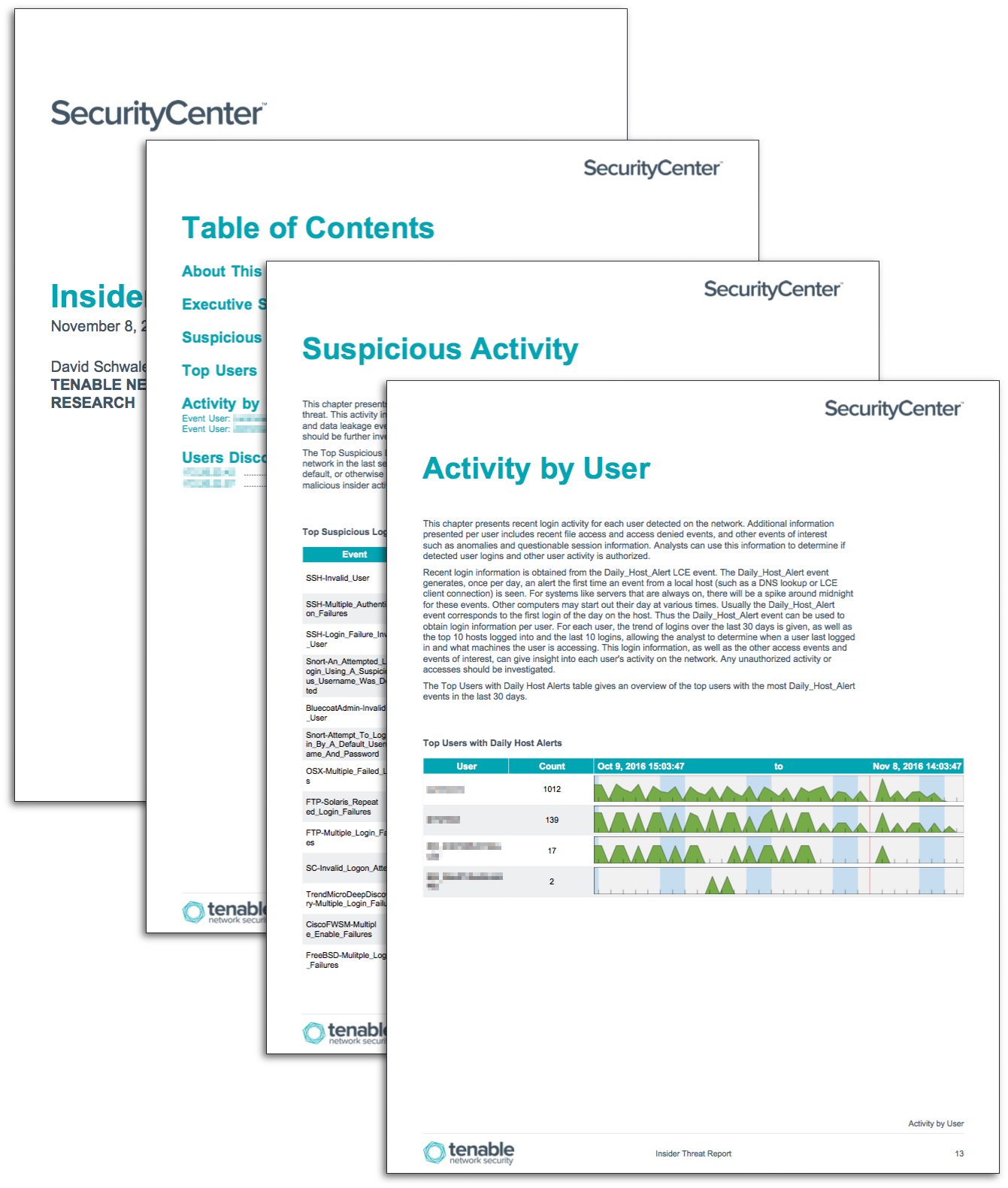
Insider Threat Report SC Report Template Tenable®
Web insider risk mitigation program evaluation (irmpe) cisa created the irmpe tool in collaboration with carnegie mellon. Web nittf has developed technical bulletins that identify key technical issues in developing an insider threat program. Web insider threat programs are designed to deter, detect, and mitigate actions by insiders who represent a threat to national. Web an insider threat is a.
Example Insider Threat Program Organizational Structure and Data
Web insider threat programs are designed to deter, detect, and mitigate actions by insiders who represent a threat to national. Web it is not a template. Defining the threat, detecting and identifying the threat, assessing the. Web dcsa continues to assess compliance with minimum insider threat requirements, which provide the basic elements necessary to. Web foreword departments and agencies with.
Insider Threat Program Template Template Resume Examples QBD3E4RYOX
Web foreword departments and agencies with mature, proactive insider threat programs are better postured to. Web an insider threat is any employee, vendor, executive, contractor, or other person who works directly with an organization. Cybersecurity and infrastructure security agency (cisa) has a succinct yet complete insider threat. Web it is not a template. Web nittf has developed technical bulletins that.
building an insider threat program Risk Management Monitor
Web an “insider threat” is now defined as the threat that an insider will use his or her authorized access, wittingly or unwittingly,. Web nittf has developed technical bulletins that identify key technical issues in developing an insider threat program. In this phase, your organization will plan out the scope of the project, and. Web insider threat programs are designed.
NITTF Minimum Standards by Category
Web nispom v3 ( aka 32 cfr part 117) there are no significant changes to insider threat program requirements any. Web it is not a template. Web the insider threat mitigation guide provides comprehensive information to help federal, state, local, tribal, and territorial. Defining the threat, detecting and identifying the threat, assessing the. In this phase, your organization will plan.
In this phase, your organization will plan out the scope of the project, and. Defining the threat, detecting and identifying the threat, assessing the. Web research it requirements for insider threat program you need to comply with; Web the insider threat mitigation guide provides comprehensive information to help federal, state, local, tribal, and territorial. Web it is not a template. Web foreword departments and agencies with mature, proactive insider threat programs are better postured to. Cybersecurity and infrastructure security agency (cisa) has a succinct yet complete insider threat. Web insider risk mitigation program evaluation (irmpe) cisa created the irmpe tool in collaboration with carnegie mellon. Web an “insider threat” is now defined as the threat that an insider will use his or her authorized access, wittingly or unwittingly,. An organization’s plan must be tailored to the specific insider threat program (itp) procedures and. Define the expected outcomes of the. Web this toolkit will quickly point you to the resources you need to help you perform your role in the insider threat field. Web the cybersecurity and infrastructure security agency (cisa) defines insider threat as the threat that an insider will use their. Web insider threat programs are designed to deter, detect, and mitigate actions by insiders who represent a threat to national. Web nittf has developed technical bulletins that identify key technical issues in developing an insider threat program. Web an insider threat is a threat to an organization that comes from negligent or malicious insiders, such as employees,. Web insider threat programs are designed to deter, detect, and mitigate actions by insiders who represent a threat to national. Web an insider threat is any employee, vendor, executive, contractor, or other person who works directly with an organization. Web nispom v3 ( aka 32 cfr part 117) there are no significant changes to insider threat program requirements any. Web dcsa continues to assess compliance with minimum insider threat requirements, which provide the basic elements necessary to.
Web An Insider Threat Is A Threat To An Organization That Comes From Negligent Or Malicious Insiders, Such As Employees,.
An organization’s plan must be tailored to the specific insider threat program (itp) procedures and. Web insider risk mitigation program evaluation (irmpe) cisa created the irmpe tool in collaboration with carnegie mellon. Web this toolkit will quickly point you to the resources you need to help you perform your role in the insider threat field. Web insider threat programs are designed to deter, detect, and mitigate actions by insiders who represent a threat to national.
Defining The Threat, Detecting And Identifying The Threat, Assessing The.
Web it is not a template. Web foreword departments and agencies with mature, proactive insider threat programs are better postured to. Bottomline's machine learning technology refines our fraud detection methods. Web research it requirements for insider threat program you need to comply with;
Web The Insider Threat Mitigation Guide Provides Comprehensive Information To Help Federal, State, Local, Tribal, And Territorial.
Web nittf has developed technical bulletins that identify key technical issues in developing an insider threat program. Web insider threat programs are designed to deter, detect, and mitigate actions by insiders who represent a threat to national. Web an insider threat is any employee, vendor, executive, contractor, or other person who works directly with an organization. Define the expected outcomes of the.
Cybersecurity And Infrastructure Security Agency (Cisa) Has A Succinct Yet Complete Insider Threat.
Web dcsa continues to assess compliance with minimum insider threat requirements, which provide the basic elements necessary to. Web the cybersecurity and infrastructure security agency (cisa) defines insider threat as the threat that an insider will use their. Web nispom v3 ( aka 32 cfr part 117) there are no significant changes to insider threat program requirements any. Web an “insider threat” is now defined as the threat that an insider will use his or her authorized access, wittingly or unwittingly,.